Automate Document Signing using the DocuSign API
Adam Yue
Jan. 29, 2020
/
As you may have noticed, Red Hat replaces the docker daemon with CRI-O/Podman since RHEL 8. So what is Podman? According to the definition at Podman official website,
Podman is a daemonless container engine for developing, managing, and running OCI Containers on your Linux System. Containers can either be run as root or in rootless mode.
Why does Red Hat want to get rid of the Docker Daemon? This is because there are few problems with running Docker with Docker Daemon
So Podman solves the above issues by directly interacting with Image registry, containers and image storage instead of work through a daemon. And the rootless mode allows a user to run containers without the full root authority. Besides, it also provides a Docker compatible command-line experience enabling users to pull, build, push and run containers.
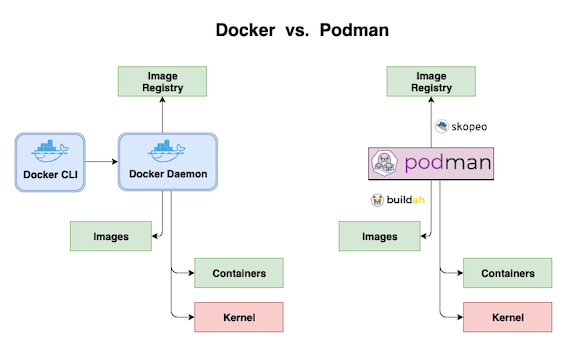
Podman interacts with Linux kernel to manage containers through the runC container runtime process instead of a daemon . The buildah utility is used to replace Docker build as the container images build tool and Docker push is replaced by skopeo for moving container images between registries and container engines.
For RHEL7, subscribe rhel-7-server-extras-rpms yum repository and then enable Extras channel and install Podman.
sudo subscription-manager repos --enable=rhel-7-server-extras-rpms
sudo yum -y install podmanPodman supports rootless mode, for more details to set up rootless mode on Redhat 7, please refer: https://www.redhat.com/en/blog/preview-running-containers-without-root-rhel-76
This article will focus on the basic usage of Podman.
Most Podman commands are similar to Docker commands. If you’ve used the Docker CLI, you will be quite familiar with Podman.
# Pull mage
sudo podman pull nginx
# List images
sudo podman images
# Run container
sudo podman run -dt -p 8081:80/tcp -v /opt/http:/usr/share/nginx/html:ro --name hello-nginx nginx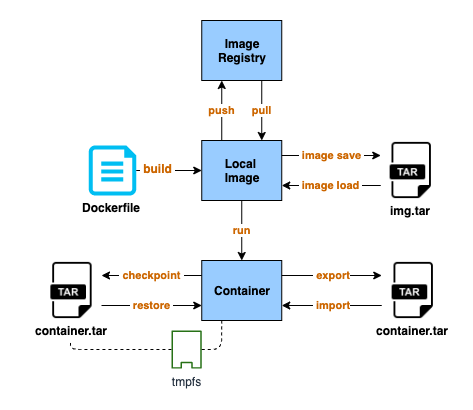
If you running containers with tmpfs volume, then
export/import can not be the backup solution for that container because
export does not back up the memory content. The files in the
tmpfs volume will be lost when you import the container from
the tar file. Here is checkpoint/restore come in. For docker,
you need to turn on the experimantal feature to enable the feature. Podman
can use these features directly without doing any change.
The criu package is required to do checkpoint/restore. And
you have to add --security-opt="seccomp=unconfined" when running a
container on RHEL because CRIU cannot correctly handle seccomp on RHEL7
sudo yum install -y criu
sudo podman run -dt --tmpfs /tmp -v /opt/http:/usr/share/nginx/html --security-opt="seccomp=unconfined" --name hello-nginx nginxsudo podman exec -it hello-nginx touch /tmp/test-01sudo podman container checkpoint --leave-running --export=/tmp/backup.tar hello-nginxsudo podman stop hello-nginx
sudo podman rm hello-nginx
sudo podman container restore --import=/tmp/backup.tar$ sudo podman exec -it hello-nginx ls /tmp/test-01
/tmp/test-01As the replacement of Docker, Podman provides the same developer experience as Docker while doing things in a slightly more secure way in the background. You could alias Docker with Podman and never notice that there is a completely different tool for managing your local containers. Besides, with the daemonless design and the rootless mode, Podman is a bit more isolated and more secure to use than Docker. You should consider using Podman instead of installing Docker-ce on your local machine.
Address
Level 8
11-17 York Street
Sydney NSW 2000
Phone Number
+61 2 8294 8067
Email
[email protected]

By Adam Yue
By Felix Schmitz
© 2017-2024 Darumatic Pty Ltd. All Rights Reserved.